Ransomware is a type of malware (malicious software) that cybercriminals use to hold people to ransom.
A ransomware attack is where an individual or organization is targeted with ransomware. It can be spread to computers through attachments or links in phishing emails, by infected web sites by means of a drive-by download or via infected USB sticks.
Once a computer or network is infected with ransomware, the malware blocks access to the system or encrypt the data on that system. Cybercriminals demand that the victims pay a ransom in order to regain access to their computer or data.
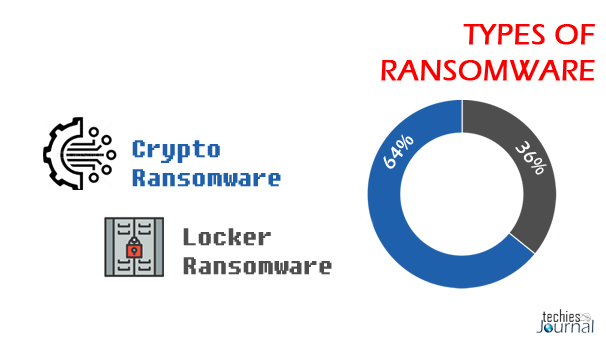
Types of Ransomware
There are two main types of ransomware
- Crypto ransomware
- Locker ransomware
Crypto ransomware encrypts valuable files on a computer so that the victim cannot access them.
Cyberthieves that conduct crypto-ransomware attacks make money by demanding that victims pay a ransom to get their files back.
Locker ransomware does not encrypt files. Rather, it locks the victim out of their device, preventing them from using it. Once they are locked out, cybercriminals carrying out locker ransomware attacks will demand a ransom to unlock the device.
Examples of Ransomware
CryptoLocker
CryptoLocker botnet is one of the oldest forms of cyber-attacks that have been around for the past two decades. The CryptoLocker ransomware came into existence in 2013 when hackers used the original CryptoLocker botnet approach in ransomware.
CryptoLocker is the most destructive form of ransomware since it uses strong encryption algorithms. It is often impossible to decrypt (restore) the Crypto ransomware-infected computer and files without paying the ransom.
WannaCry
WannaCry is the most widely known ransomware variant across the globe in 2017.
Designed to exploit a vulnerability in Windows, it was allegedly created by the United States National Security Agency and leaked by the Shadow Brokers group. WannaCry affected 230,000 computers globally.
The global financial impact of WannaCry was substantial -the cybercrime caused an estimated $4 billion in financial losses worldwide.
Some of the alternative names given to the WannaCry ransomware are WCry or WanaCrypt0r.
Bad Rabbit
Bad Rabbit is a 2017 ransomware attack that spread using a method called a ‘drive-by’ attack, where insecure websites are targeted and used to carry out an attack.
Drive-by attacks often require no action from the victim, beyond browsing to the compromised page. However, in this case, they are infected when they click to install something that is actually malware in disguise. This element is known as a malware dropper.
Bad Rabbit used a fake request to install Adobe Flash as a malware dropper to spread its infection.
Ryuk
Ryuk ransomware, which spread in August 2018, disabled the Windows System Restore option, making it impossible to restore encrypted files without a backup.
Ryuk also encrypted network drives.
Troldesh
The Troldesh ransomware attack happened in 2015 and was spread via spam emails with infected links or attachments.
Interestingly, the Troldesh attackers communicated with victims directly over email to demand ransoms. The cybercriminals even negotiated discounts for victims who they built a rapport with — a rare occurrence indeed.
This tale is definitely the exception, not the rule. It is never a good idea to negotiate with cybercriminals. Avoid paying the demanded ransom at all costs as doing so only encourages this form of cybercrime.
Crysis
Crysis is a special type of ransomware that encrypts files on fixed drives, removable drives, and network drives. It spreads through malicious email attachments with double-file extension. It uses strong encryption algorithms making it difficult to decrypt within a fair amount of time.
CryptoWall
CryptoWall is an advanced form of CryptoLocker ransomware. It came into existence since early 2014 after the downfall of the original CryptoLocker variant. Today, there are multiple variants of CryptoWall in existence. It includes CryptoDefense, CryptoBit, CryptoWall 2.0, and CryptoWall 3.0.
Petya
Petya (not to be confused with ExPetr) is a ransomware attack that first hit in 2016 and resurged in 2017 as GoldenEye.
Rather than encrypting specific files, this vicious ransomware encrypts the victim’s entire hard drive. It does this by encrypting the Master File Table (MFT) making it impossible to access files on the disk.
Petya spread through HR departments via a fake job application email with an infected Dropbox link.
GoldenEye
GoldenEye is similar to the infamous Petya ransomware. It spreads through a massive social engineering campaign that targets human resources departments. When a user downloads a GoldenEye-infected file, it silently launches a macro that encrypts files on the victim’s computer.
GandCrab
GandCrab is a rather unsavory ransomware attack that threatened to reveal the victim’s porn-watching habits.
Claiming to have highjacked users webcam, GandCrab cybercriminals demanded a ransom, or otherwise they would make the embarrassing footage public.
After having first hit in January 2018, GandCrab evolved into multiple versions. As part of the No More Ransom Initiative, internet security providers and the police collaborated to develop a ransomware decryptor to rescue victim’s sensitive data from GandCrab.
Jigsaw
Jigsaw is one of the most destructive types of ransomware which encrypts and progressively deletes the encrypted files until a ransom is paid. It starts deleting the files one after the other on an hourly basis until the 72-hour mark- when all the remaining files are deleted.
Locky
Locky is another ransomware variant that is designed to lock the victim’s computer and prevent them from using it until a ransom is paid. It usually spread through a seemingly benign email message disguised as an invoice.
When a user opens the email attachment, the invoice gets deleted automatically, and the victim is directed to enable macros to read the document. When the victim enables macros, Locky begins encrypting multiple file types using AES encryption.
Apart from the list of attacks mentioned above NotPetya, TeslaCrypt, TorrentLocker, ZCryptor, etc., are some of the other ransomware variants that are well-known for their malicious activities.
More Information about Ransomware
What is Ransomware? How it works? How Prevent an Attack?