Security researchers at South Korean cybersecurity firm ESTsecurity have discovered a new strain of Android Trojan KevDroid that is being distributed disguised as a fake anti-virus application, dubbed “Naver Defender.”
Dubbed KevDroid, the mobile threat can steal contacts, messages, and phone history, while also able to record phone calls, Talos reports. Two variants of the malware have been identified so far.
One of the variants exploits CVE-2015-3636 to gain root access, but both implement the same call recording capabilities, taken from an open-source project on GitHub.
Once it has infected a device, the first KevDroid variant can gather and siphon information such as installed applications, phone number, phone unique ID, location, stored contacts information, stored SMS, call logs, stored emails, and photos.
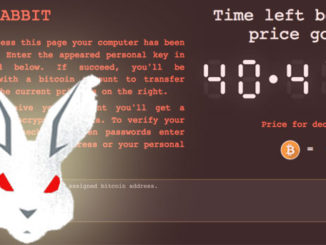
A new piece of Android malware has been discovered. Dubbed KevDroid, the malware is being distributed in the form of a fake anti-virus application called Naver Defender. KevDroid is in fact a remote administration tool that steals sensitive data from infected devices. However, the malware is also capable of recording phone calls.
Large in size, the second variant of the malware was hosted at the same URL in February, and has been observed using SQLite databases to store data. It includes the same data gathering capabilities, along with camera recording, audio recording, web history stealing, file stealing, and the ability to gain root on the device.
An ELF file embedded in the APK attempts to exploit the CVE-2015-3636 vulnerability using code available on GitHub to obtain root permission. By gaining higher privileges, the malware can perform more in-depth actions, including stealing files from other applications.
Attackers could also blackmail victims using images or information deemed secret, could steal credentials and multi-factor tokens (SMS MFA), and could also engage in banking/financial fraud using their access to privileged information. Should the infected device be used in corporate environments, a KevDroid attack could lead to cyber espionage More About KevDroid
How to Keep Your Smartphone Secure
Android users are advised to regularly cross-check apps installed on their devices to find and remove if any malicious/unknown/unnecessary app is there in the list without your knowledge or consent.
- Never install applications from 3rd-party stores.
- Ensure that you have already opted for Google Play Protect.
- Enable ‘verify apps’ feature from settings.
- Keep “unknown sources” disabled while not using it.
- Install anti-virus and security software from a well-known cybersecurity vendor.
- Regularly back up your phone.
- Always use an encryption application for protecting any sensitive information on your phone.
- Never open documents that you are not expecting, even if it looks like it’s from someone you know.
- Protect your devices with pin or password lock so that nobody can gain unauthorized access to your device when remains unattended.
- Keep your device always up-to-date with the latest security patches.