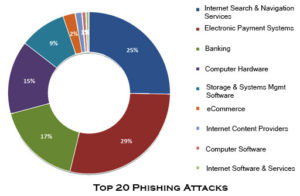
Cybercrime has shown its teeth in the last five years, most predominantly, in the online fraud cases caused by phishing. Have you ever noticed why you are receiving increasing number of spam or fake emails every day?
Phishing is an attempt by an individual or group to solicit personal information from unsuspecting users by employing social engineering techniques. Phishing emails are crafted to appear as if they have been sent from a legitimate organization or known individual.
These emails often attempt to entice users to click on a link that will take the user to a fraudulent website that appears legitimate. The user then may be asked to provide personal information, such as account usernames and passwords, that can further expose them to future compromises. Additionally, these fraudulent websites may contain malicious code.
The goal of a phishing attempt is to trick the recipient into taking the attacker’s desired action, such as providing login credentials or other sensitive information. For instance, a phishing email appearing to come from a bank may warn the recipient that their account information has been compromised, directing the individual to a website where their username and/or password can be reset. This website is also fraudulent, designed to look legitimate, but exists solely to collect login information from phishing victims.
These fraudulent websites may also contain malicious code which executes on the user’s local machine when a link is clicked from a phishing email to open the website.
Companies are bombarded with phishing scams every day. In a recent survey of more than 500 cyber security professionals across the world, 76% reported that their organization fell victim to a phishing attack.
Phishing types
Spear phishing
Phishing attempts directed at specific individuals or companies have been termed spear phishing. Attackers may gather personal information about their target to increase their probability of success. This technique is, by far, the most successful on the internet today, accounting for 91% of attacks.
Example: Customers of a telecommunications firm received an e-mail recently explaining a problem with their latest order. They were asked to go to the company website, via a link in the e-mail, to provide personal information—like their birth dates and Social Security numbers. But both the e-mail and the website were bogus.
Clone phishing
Clone phishing is a type of phishing attack whereby a legitimate, and previously delivered, email containing an attachment or link has had its content and recipient address(es) taken and used to create an almost identical or cloned email. The attachment or link within the email is replaced with a malicious version and then sent from an email address spoofed to appear to come from the original sender.
It may claim to be a resend of the original or an updated version to the original.
Whaling
Several phishing attacks have been directed specifically at senior executives and other high-profile targets within businesses, and the term whaling has been coined for these kinds of attacks. In the case of whaling, the masquerading web page/email will take a more serious executive-level form.
The content will be crafted to target an upper manager and the person’s role in the company. The content of a whaling attack email is often written as a legal subpoena, customer complaint, or executive issue.
Whaling scam emails are designed to masquerade as a critical business email, sent from a legitimate business authority. The content is meant to be tailored for upper management, and usually involves some kind of falsified company-wide concern.
How Phishing Attacks Harm. Business/Individuals?
Phishing is a serious crime in the cyber world. Due to Phishing, there may be
- financial loss
- data loss
- blacklisting of institutions
- introduction of malware and viruses into a PC or a computer system
- illegal use of user’s details
- misuse of your social security number
 The phisher can also take a user’s account details and open a new account on the name of the user for financial gain. Phishing can even be used to ruin someone’s life by misappropriating and misusing their personal details.
The phisher can also take a user’s account details and open a new account on the name of the user for financial gain. Phishing can even be used to ruin someone’s life by misappropriating and misusing their personal details.
Protection against Phishing Attacks
It is advisable to keep our eyes open against phishing. Here are some steps that might be helpful to prevent you from being part of the statistics.
Two-Factor Authentication
Gmail, Facebook, Dropbox, Microsoft, Yahoo and Apple’s iCloud is using two-factor authentication. In this process you login with a password and a secret code you will receive on your mobile phone so unless the hacker has access to your mobile too, having just your email and your password is not enough to break into your account.
How to prevent phishing
|
|---|
HTTPS instead of HTTP
HTTPS is a more secure protocol than HTTP as it encrypts your browser and all the information you send or receive. If you are looking to make online payments or transactions, opt for an HTTPS website. Such HTTPS websites are equipped with SSL (secure socket layer) that creates a secure channel for information transition.
Website Reliability
With Phishing, hackers can create a similar website with a normal-looking login page where users enter login details or even credit card details. Therefore, before entering login details users has to check the padlock appeared on the top or bottom of webpage.
Anti-Spam Software
With use of anti-spam software user can reduce phishing attacks. Users can control spam mail thus securing himself from phishing. This software can also help with browser hijacking, usually finding the problem and providing a solution.
Hyperlink in Email
Never click hyperlinks received in emails from an unknown or unverified source. Such links contain malicious codes and you be asked for login details or personal information when you reach the page you are led to from the hyperlink.
Firewall
With a firewall, users can prevent many browser hijacks. It is important to have both desktop and network firewalls as firewalls check where the traffic is coming from, whether it is an acceptable domain name or Internet protocol. It is also effective against virus attacks and spyware.