A Distributed Denial of Service (DDoS) attack is an attempt to make an online service unavailable by overwhelming it with traffic from multiple sources.
Recent studies have found that nearly three fourths of major organizations worldwide would have experienced Distributed Denial of service (DDoS) attacks. Volumetric DDoS are been designed specifically to consume your network bandwidth, thereby congesting your network/system, and possibly ending up crashing your network infrastructure.
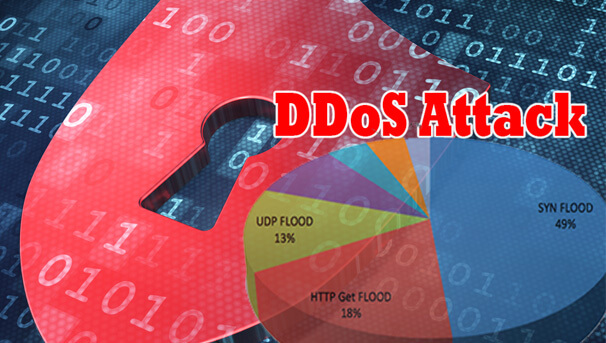
DDoS attacks are normally initiated through mechanisms such as UDP flood, DNS amplification, etc. This makes prevention quite difficult.
How DDoS Attacks Work
In a DDoS attack, the incoming traffic flooding the victim originates from many different sources – potentially hundreds of thousands or more. This effectively makes it impossible to stop the attack simply by blocking a single IP address; plus, it is very difficult to distinguish legitimate user traffic from attack traffic when spread across so many points of origin.
DoS and DDos
A Denial of Service (DoS) attack is different from a DDoS attack. The DoS attack typically uses one computer and one Internet connection to flood a targeted system or resource. The DDoS attack uses multiple computers and Internet connections to flood the targeted resource. DDoS attacks are often global attacks, distributed via botnets.
DDoS Attacks
There are many types of DDoS attacks. Common attacks include the following:
Traffic attacks: Traffic flooding attacks send a huge volume of TCP, UDP and ICPM packets to the target. Legitimate requests get lost and these attacks may be accompanied by malware exploitation.
Bandwidth attacks: This DDos attack overloads the target with massive amounts of junk data. This results in a loss of network bandwidth and equipment resources and can lead to a complete denial of service.
Application attacks: Application-layer data messages can deplete resources in the application layer, leaving the target’s system services unavailable.
