
Fingerprint sensors have turned modern smartphones into miracles of convenience. A touch of a finger unlocks the phone.
New findings published by researchers at New York University and Michigan State University suggest that smartphones can easily be fooled by fake fingerprints digitally composed of many common features found in human prints. In computer simulations, the researchers from the universities were able to develop a set of artificial “MasterPrints” that could match real prints similar to those used by phones as much as 65 percent of the time.
The researchers did not test their approach with real phones, and other security experts said the match rate would be significantly lower in real-life conditions. Still, the findings raise troubling questions about the effectiveness of fingerprint security on smartphones.
Full human fingerprints are difficult to falsify, but the finger scanners on phones are so small that they read only partial fingerprints. When a user sets up fingerprint security on an Apple iPhone or Android Phone, the phone typically takes eight to 10 images of a finger to make it easier to make a match. And many users record more than one finger — say, the thumb and forefinger of each hand.
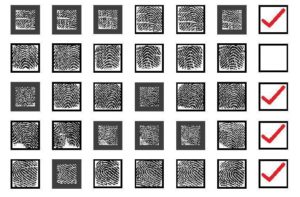
Since a finger swipe has to match only one stored image to unlock the phone, the system is vulnerable to false matches.
“It’s as if you have 30 passwords and the attacker only has to match one,” said Nasir Memon, a professor of computer science and engineering at N.Y.U.’s Tandon School of Engineering, who is one of three authors of the study, which was published in IEEE Transactions on Information Forensics and Security. The other authors are Aditi Roy, a postdoctoral fellow at N.Y.U.’s Tandon School, and Arun Ross, a professor of computer science and engineering at Michigan State.
Dr. Memon said their findings indicated that if you could somehow create a magic glove with a MasterPrint on each finger, you could get into 40 to 50 percent of iPhones within the five tries allowed before the phone demands the numeric password, known as a personal identification number.
Stephanie Schuckers, a professor at Clarkson University and director of the Center for Identification Technology Research, was cautious about the implications of the MasterPrint findings. She said the researchers used a midrange, commercially available software program that was designed to match full fingerprints, limiting the broader applicability of their findings.
“To really know what the impact would be on a cellphone, you’d have to try it on the cellphone,” she said. She noted that cellphone makers and others who use fingerprint security systems are studying anti-spoofing techniques to detect the presence of a real finger, such as looking for perspiration or examining patterns in deeper layers of skin. A new fingerprint sensor from Qualcomm, for example, uses ultrasound.
Phone makers have acknowledged that fingerprint sensors are not foolproof, but said that the ease of touching a finger to unlock a phone meant that more users actually turned on security features instead of leaving their phones unlocked — a common habit in the early days of smartphones.
Identity theft, fraud and terrorism are real problems. Used properly, biometrics could help protect against them. But the potential for misuse is glaringly obvious. We must begin setting rules to govern the use of these technologies now.
Since a finger swipe has to match only one stored image to unlock the phone, the system is vulnerable to false matches.
